Alert Manager Enterprise for Electric Utilities: Simplifying NERC CIP Compliance Inside Splunk

Electric utilities face some of the world's strictest cybersecurity mandates. NERC CIP standards require continuous monitoring, rigorous access controls, fully auditable incident handling, and strict separation of critical assets - all without ever moving sensitive data outside your secure perimeter.
Alert Manager Enterprise (AME) helps grid operators meet these requirements with a structured, auditable alert lifecycle that stays entirely inside their existing Splunk environment.
If you already use Splunk for visibility and alerting, AME turns your current Splunk alerts into compliant workflows - without external tools, data egress, or heavy custom development.
No new consoles. No compliance gaps. Just reliable event management that supports grid protection and simplifies audits.
The Reality for Utility SOC and Operations Teams
Splunk is already used in many utility environments for visibility and alerting. Yet turning raw alerts into compliant, team-ready event workflows remains challenging:
- Teams must see only the events and assets relevant to their role
- NERC vs. non-NERC assets and data needs clear separation
- Triage, assignment, annotation, and status tracking must happen inside the secure NERC perimeter
- Full change history and exportable records are essential for audits
- Manual tracking of alert ownership, comments, and status changes often leads to incomplete audit evidence and findings during NERC audits
External incident management tools introduce compliance friction (data egress, scope expansion). Heavy custom development inside Splunk often becomes fragile over time.
Alert Manager Enterprise - Built for Electric Utilities
Our AME App is a native Splunk application that helps regulated grid operators manage alerts and events effectively. It integrates directly into Splunk Enterprise and Splunk Cloud. This means that your alerts and events stay in Splunk, and management happens within the same environment.
AME elevates standard Splunk alerts into a structured, auditable lifecycle that supports NERC CIP requirements while reducing manual effort for operations, security, and compliance teams. For a deeper look at day-to-day event handling, see the documentation on working with events.
A key strength for utilities is the Observables framework, which lets you manage assets and identities by tenant. Observables are used to enrich events with asset and identity information (e.g. asset owner, criticality, location and so on). This provides deeper asset context per team or asset group, strengthens correlation for investigations, and aligns perfectly with CIP-002 asset categorization and CIP-007 monitoring needs - all while maintaining strict multitenancy isolation.
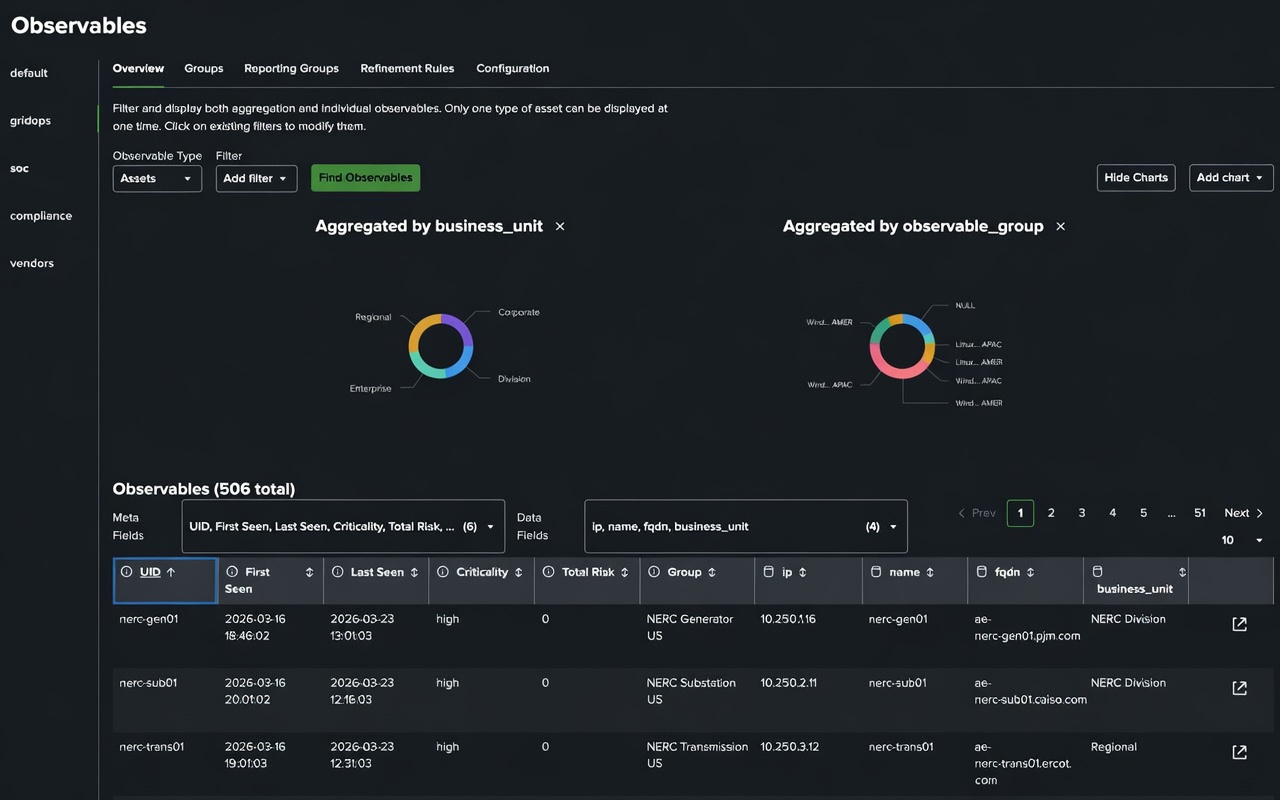
AME Observables enrich events with asset and identity context while preserving tenant isolation.
Key alignments utilities rely on:
| NERC CIP Standard | Focus Area | Core Obligation | How AME Delivers | Everyday Value for Utility Teams |
|---|---|---|---|---|
| CIP-005-7 | Electronic Security Perimeter | Strict electronic security perimeters and controlled access to BES Cyber Systems | Multitenancy + granular RBAC on events | Teams view only their assigned assets; oversight roles maintain full visibility without violating rules |
| CIP-007-6 | Systems Security Management | Systems security management, access control, and need-to-know principles | Multitenancy + granular RBAC on events | Teams view only their assigned assets; oversight roles maintain full visibility without violating rules |
| CIP-002-5.1a | Asset Categorization | Identification and categorization of BES Cyber Systems | Dedicated dashboards with simple BES Cyber System / non-BES toggles (High/Medium/Low impact) | Clean, focused views for grid operations; no endless searching |
| CIP-007-6 | Event Monitoring & Detection | Continuous monitoring, logging, and detection of events on BES Cyber Systems | Live dashboards, automatic deduplication, Security Pack (MITRE ATT&CK mapping, risk scoring) | Prioritized, lower-noise alerts; quicker anomaly response |
| CIP-015-1 | Internal Network Security Monitoring (INSM) | Security event logging, analysis, and detection of anomalous activity inside Electronic Security Perimeters | Live dashboards, automatic deduplication, Security Pack (MITRE ATT&CK mapping, risk scoring) | Prioritized, lower-noise alerts; quicker anomaly response and improved dwell-time detection |
| CIP-008-6 | Incident Reporting & Response | Review, triage, document, and track Cyber Security Incidents | Native Splunk lifecycle: assign, comment, tag, update status, link observables | Full triage and annotation stays inside the compliant Splunk instance |
| CIP-008-6 | Response & Audit Evidence | Timely notifications, traceable actions, and evidence for reporting | SLA timers, multi-channel notifications, complete per-event history | Defensible, export-ready audit trails with one-click evidence packages — dramatically reducing audit preparation time |
| CIP-003-9 | Vendor Remote Access Oversight | Oversight of vendor electronic remote access, including detection of malicious communications | Scoped views and alerts for vendor-related activity | Early awareness of vendor access/activity without introducing new tools or expanding attack surface |
SLA Management & Enterprise Ticketing Integration
AME includes built-in SLA timers with visual countdowns, escalation rules, and automated notifications - giving operations and compliance teams clear visibility into response deadlines. This directly supports timely incident handling under NERC CIP-008 while reducing the risk of missed SLAs during audits.
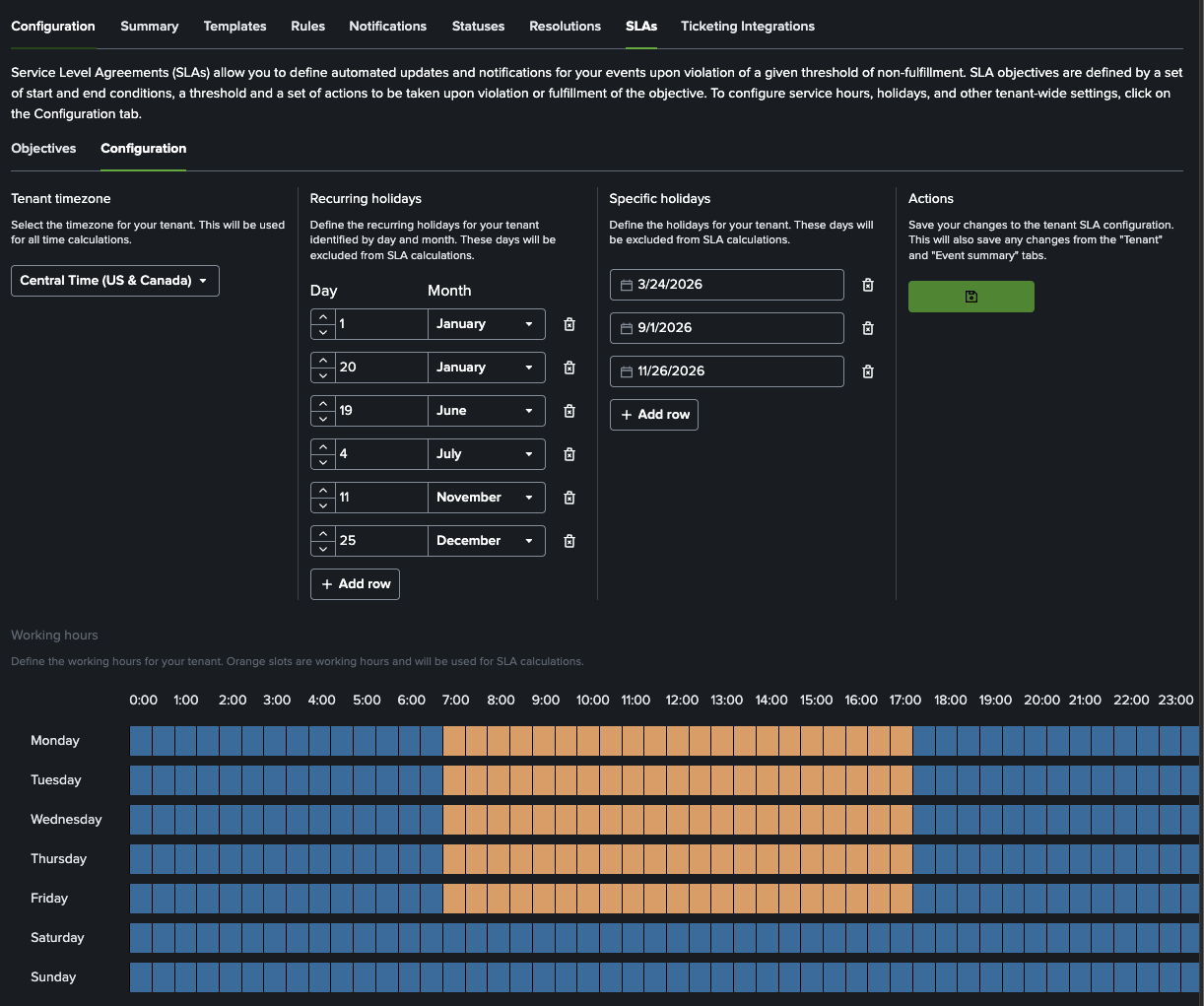
Built-in SLA timers make response deadlines visible and easier to defend during audits.
For utilities that still need to create tickets in Jira or ServiceNow, AME offers native ticketing integration. Events can be pushed to the ticketing platform with full context and observables, while status updates (e.g. “Resolved”, “Closed”) are automatically synced back into Splunk - keeping the authoritative audit trail inside your secure Splunk environment.
This hybrid approach gives you the best of both worlds: compliant, auditable workflow management in Splunk + seamless process alignment with the rest of the enterprise.
AME works by adding an Alert Action to your existing Splunk searches. Alerts trigger and are turned into events that are managed in the Splunk UI. Notifications and event automation can integrate externally when needed, but core event data and management remain in Splunk. It integrates seamlessly with your current Splunk alerts, searches, and retention settings, helping shift compliance from a separate task to an integrated part of daily grid protection work.
If your utility manages segmented teams, needs traceable alert workflows, or is preparing for evolving CIP requirements, AME offers a practical, low-friction path forward.
Ready to see it in action?
- Download the free Community Edition directly from Splunkbase
- Request a 30-day Enterprise trial license tailored for utilities
- Book a focused demo with our specialists
Alert Manager Enterprise - Event management that keeps your grid reliable, your team efficient, and your auditors happy.